Network Defense Intelligence
 Troves of documents on public-facing websites expose content and metadata to dedicated adversaries and other third parties for discovery, harvesting, and analysis, which can reveal privileged details about an organization or individual. Unfortunately, most if not all organizations fail to protect this data or are unaware this is an issue of major concern – until there’s been a breach.
Troves of documents on public-facing websites expose content and metadata to dedicated adversaries and other third parties for discovery, harvesting, and analysis, which can reveal privileged details about an organization or individual. Unfortunately, most if not all organizations fail to protect this data or are unaware this is an issue of major concern – until there’s been a breach.
IDP helps clients to cost-effectively identify their areas of vulnerability and potential leaks, adopt safe practices, and secure their documents and content from competitors and bad actors.
IDP offers the following services:
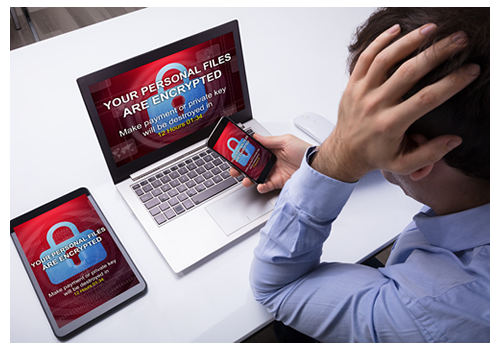
Cyber Threat Intelligence (CTI) Cyber threat actors, including nation-states and cyber criminals routinely scan computer networks, seeking vulnerable entry points to exploit. IDP’s CTI services set up “lookalike” computer servers, enticing hackers to direct their attention away from your actual infrastructure. IDP then delivers cyber indicators, of highly specific, precise threat intelligence of how attackers are actually trying to penetrate your organization.
Vulnerability Management (VM) IDP monitors newly disclosed software vulnerabilities, plus the activities of criminal hacking organizations. After learning the precise software platforms, operating systems, and hardware that runs your enterprise network, IDP VM alerts you of only specific vulnerabilities that actually threaten your organization. This allows you to prioritize patching cycles, migration schedules, and maximize limited resources with intelligence and precision, managing to the actual threat.
Advanced Information Defense (AID) IDP’s AID scans reveal that most Fortune 500 organizations, plus the companies entrusted to protect their networks fail to tackle information leaks from metadata and document track changes. Frequently, IDP identifies company proprietary data still preserved in Office and PDF documents that can easily be exploited by competitors and other malicious actors to penetrate information networks. Unfortunately companies rarely have any idea they are actually leaking valuable details about their employees, network, software. Why should others gain strategic advantage by stealing your intellectual property right from your own documents? AID is a unique capability that locates and works with clients to mitigate vulnerabilities to organizations caused by inadvertent leakage of sensitive metadata and other information.
